Brownies is loved by everyone, specially this fudge brownies is a family favorite. Delicious fudgy brownies made with basic ingredients like flour, cocoa, sugar, brown sugar, eggs and butter which creates a moist gooey texture. Few tips is shared in this brownie recipe post to achieve shiny exterior and fudgy interior. Learn how to make the perfect brownies with step by step pictures and video.

Fudge Brownies
If you are a regular viewer of mine, you all know how much I love making brownies. I have over 40 recipes for different flavour brownies in this blog which I have shared over the years. But this recipe is one of my top favorite and this is the recipe which I make over and over again.
About Fudge Brownies Recipe
This is one of the best fudgy chocolate brownies with the gooey centre and crispy crackly top. If you are hosting a party or if you want to make something for a get together then this brownies is spot on.
Brownies are a rich decadent chocolate dessert which takes less than an hour to make from start to finish. This brownies is made with basic ingredients like butter, sugar, brown sugar, cocoa, flour and eggs.
The moist and fudge texture is achieved by melted butter and chopped chocolate chunks which is added in the brownie batter. To achieve the perfect shiny texture, make sure you read my tips section.
The brownie taste amazing warm with a scoop of chocolate ice cream, chocolate sauce & butterscotch sauce.
Watch Fudge Brownies Video

Brownies Ingredients

Plain Flour - I used refined flour also known as all purpose flour or maida for making the brownies. This gives the perfect texture in the brownies. But you can use wheat flour or half wheat flour and half portion of plain flour as well.
Cocoa - This is a cocoa based brownies. So use the best quality cocoa powder that you can find.
Sugar - a combination of brown sugar and white sugar is used in the brownies to create fudgy texture.
Vanilla - pure vanilla extract is preferred for the flavour.
Chocolate Bar - Chopped chocolate is scattered all over the brownies. I like to use good quality milk chocolate. When you bite into a piece of brownie, this chocolate adds rich taste.
Eggs - eggs are main ingredient in this brownie and it cannot be made without eggs. But you can check my eggless brownies for egg free option.
Instant Coffee - coffee when combined with chocolate gives an intense chocolate flavour. You won't taste the coffee in the brownies. Instead it makes the brownies so chocolaty.
Butter - good quality butter is melted and used in this brownies. I strongly recommend you to use butter and not oil.
Salt - salt balance the taste of the sugar and chocolate.

Fudgy Chocolate Brownies in 3 Easy Steps
Pre-preparation
Use 9x10 baking tray lined with parchment paper. Melt butter in microwave or stove top. Preheat oven to 180 degree C.
Brownie Batter
Mix melted butter, brown sugar, sugar, vanilla, coffee and eggs till creamy and frothy. Add in flour, cocoa power and fold gently. Finally fold in chopped chocolate.
Baking Fudgy Brownies
Bake in preheated oven for 25 to 30 minutes. Remove it from oven, cool it for few minutes. Slice and serve.
Try these amazing brownies
Caramel Almond Brownies
Eggless Yogurt brownies
White Chocolate Brownies

How to Make Fudge Brownies (Stepwise Pictures)
Pre-Preparation
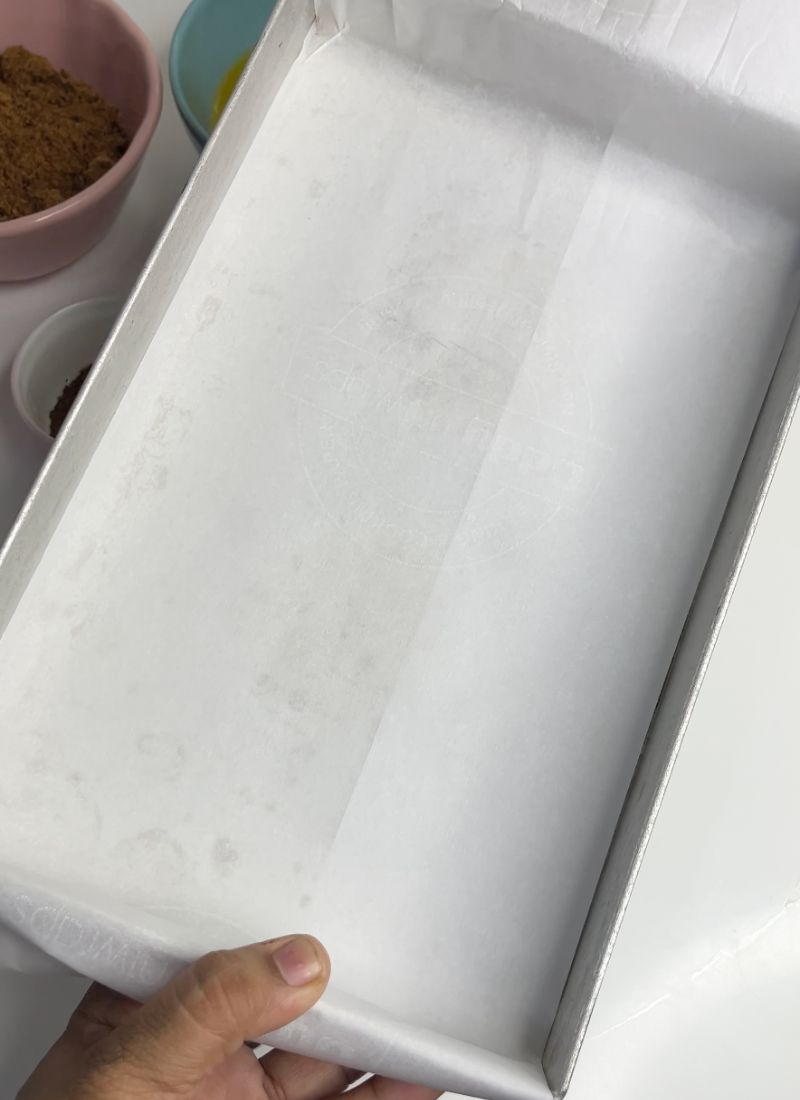
Preheat oven to 180 degree C | 356 degree F. Line a 11x7 inches rectangle pan with parchment paper. Make sure the paper is slightly over hanging the pan. Set aside till needed.
Mixing Butter with Sugar
1)Take butter in a microwave safe bowl and melted it for 30 seconds in microwave. Leave it aside for 5 minutes to cool. Now Take melted butter in a mixing bowl.

2)Add in brown sugar. In this brownie recipe, you need a combination of brown sugar and regular sugar. The brown sugar keeps the brownies super moist.

3)Add in regular sugar.

4)Add in vanilla extract. Make sure you use pure vanilla extract for flavour.

5)Add a pinch of salt into the sugar and butter mixture.

6)Now to mix you can use hand whisk to mix till combined. I like to use electric mixer for faster mixing.

7)It will take around a minute to combine.

Whisking in Eggs
8)I used three eggs, crack them in a separate bowl before adding into the butter sugar mixture.

9)Mix butter sugar and eggs till creamy and frothy. It will take 2 to 3 minutes of mixing.

10)I mixed 1 tsp Instant coffee powder with 2 tbsp of hot water. Add this coffee mix into the egg sugar mixture.

11)Whisk this for 1 minute till combined.

Brownie Batter
12)Add in plain flour and cocoa powder.

13)Mix it gently till combined into a smooth batter.

14)Add in chopped chocolate chunks. You can use dark chocolate, milk chocolate or semi sweet chocolate chips.

15)Fold the chocolate into the batter gently.

Baking Brownies
16)Line a 9x10 inch pan with parchment paper. Spoon batter into the baking pan. Spread evenly with a spatula.

17)Bake it in a 180 degree C preheated oven for 25 to 30 minutes till the top is shiny and crispy. The underneath with be gooey and moist. When you remove the brownies from oven it will look moist and it will continue to cook as it cools. So don't over bake the brownies.

18)Once the brownies is removed from oven. Let it cool for 10 minutes in the pan. Use a butter knife to release the brownies from the sides. Un mould it gently from the baking pan on a cutting board. Allow it to cool for further 10 to 15 minutes. Then slice into pieces.

19)Perfect gooey brownies ready to serve.

Tips for Shiny, Crispy & Crinkly Brownies
- Make sure the butter is melted and cooled for few minutes before adding sugar.
- Use good quality brown sugar for getting perfect texture.
- Once butter is mixed into the sugar. Add eggs and use an electric beater to mix for 2 to 3 minutes till frothy which helps in the shiny crinkly exterior.
- Don't over bake the brownies else it may get hard.
Storage & Serving
Baked brownies can be stored at room temperature for 2 to 3 days.
You can store in fridge for more than a week, warm in microwave for few seconds before serving.
Brownies are best served with a cup of black coffee. Enjoy with vanilla ice cream, chocolate sauce and caramel sauce. You can serve it as sizzling brownies.
Hungry for More Brownies
📖 Recipe Card
Fudge Brownies | Fudgy Brownies Recipe
Equipment
- 9x10 baking pan
- Electric Beater
- Mixing Bowl
- Oven or OTG
Ingredients
- 225 grams Unsalted Butter
- 1 cup Brown Sugar (200 grams)
- 1 cup Sugar (200 grams)
- 1 tsp Vanilla Extract
- 1 tsp Instant Coffee Powder
- 2 tbsp Hot Water
- 3 large Eggs
- 1 cup All Purpose Flour | Plain Flour | Maida (120 grams)
- ¾ cup Cocoa Powder (75 grams)
- 1 tsp Salt
- 1 cup Milk Chocolate chopped
Instructions
- Preheat oven to 180 degree C. Line a 9 by 10 inch pan with parchment paper and set aside.
- Take butter in a microwave safe bowl and melt it for 30 seconds in microwave. Leave it aside for 5 minutes to cool. Now Take melted butter in a mixing bowl.
- Add in brown sugar, regular sugar, salt, vanilla extract. Now to mix you can use hand whisk to mix till combined. I like to use electric mixer for faster mixing. It will take around a minute to combine.
- Add in eggs and use an electric whisk to mix for 2 to 3 minutes till frothy and mixed. Mix instant coffee with 2 tbsp of hot water. Add it into the egg butter sugar mix. Mix for another 1 minute.
- Add in flour, cocoa powder and mix for few seconds. Use a spatula to fold gently. Once the batter is mixed, Add in chopped chocolate and fold gently.
- Line a 9x10 inch pan with parchment paper. Spread evenly with a spatula. Spoon this into the prepared pan and bake for 25 to 30 mins.
- Bake it in a 180 degree C preheated oven for 25 to 30 minutes till the top is shiny and crispy. The underneath with be gooey and moist. When you remove the brownies from oven it will look moist and it will continue to cook as it cools. So don't over bake the brownies.
- Once the brownies is removed from oven. Let it cool for 10 minutes in the pan. Use a butter knife to release the brownies from the sides. Un mould it gently from the baking pan on a cutting board. Allow it to cool for further 10 to 15 minutes. Then slice into pieces. Perfect gooey brownies ready to serve.
Video

Notes
For Shiny, Crispy & Crinkly Brownies
- Make sure the butter is melted and cooled for few minutes before adding sugar.
- Use good quality brown sugar for getting perfect texture.
- Once butter is mixed into the sugar. Add eggs and use an electric beater to mix for 2 to 3 minutes till frothy which helps in the shiny crinkly exterior.
- Don't over bake the brownies else it may get hard.
Storage & Serving
Baked brownies can be stored at room temperature for 2 to 3 days. You can store in fridge for more than a week, warm in microwave for few seconds before serving. Brownies are best served with a cup of black coffee. Enjoy with vanilla ice cream, chocolate sauce and caramel sauce.Nutrition
If you have any questions not covered in this post and if you need help, leave me a comment or mail me @[email protected] and I’ll help as soon as I can.
Follow me on Instagram, Facebook,Pinterest ,Youtube and Twitter for more Yummy Tummy inspiration.
IF YOU MAKE THIS RECIPE OR ANYTHING FROM YUMMY TUMMY, MAKE SURE TO POST IT AND TAG ME SO I CAN SEE ALL OF YOUR CREATIONS!! #YUMMYTUMMYAARTHI AND @YUMMYTUMMYAARTHI ON INSTAGRAM!















Surya Devi
I made this receipy as soon as I saw it in ur video blog. It's my first try in brownies and it came out awesome😍 it's a must try receipy and very easy that we can prepare in 10min. Thanks aarthi. Keep rocking
Afia
Brown sugar 1 cup and sugar 1cup it seems to be totally 480 grams of sugar it seems to be too much sugary ..I jave doubt pleae clarify me
Aarthi
You need that to attain the fudgy texture
Afreena
Maam what is the measurement of both sugars in grams....?????please tell me
Aarthi
1 cup sugar weighs 200 grams
Ruby
Hello akka..
Can I skip or substitue coffee powder? There is no coffee powder in our home since both me and my hubby don't drink coffee. Thanks in advance:)
Aarthi
yes u can skip it.
Anju
I tried this brownie recipe and it came out super yum. Thank you!
Shalini Arumugam
To bake in stove how much minutes will it take?
Bhav
Hi, what is the measurement for 1 cup flour in grams? Thanks
Boo
Isn’t there a need for baking powder?
Aarthi
No need in this recipe
Suganya
What is the size of the baking tray you are using? for me it always comes out gooey in the middle even after baking for a long time
Aarthi
nearly 9x13 inch
Kusuma
Brownie was always been my favorite. I got a new otg oven and have been trying out many baking recipes of ur channel and happy to say every dish has turned out superb.. tried this recipe too but replaced all purpose flour with atta it really was fabulous and yummy... Thank you Arathi for all the wonderful recipe posts.. Luv u...
Aishwarya
Aarthi, do we need to bake in the middle rack with heat from top and bottom to cook evenly?
Aarthi
yes you have to bake in the middle rack.